Vault Notes are notes that are end-to-end encrypted, with their encryption password never sent to our servers. In practical terms, this means that even if a malicious employee or state/government actor somehow obtained access to the Amplenote database, a long Vault Password would render them unable to decrypt the content of your Vault Notes within a human lifetime, even if they possessed access to most advanced computing resources known. The technical aspects of how Vault Notes achieve this level of security are described below.
linkAccessing Vault Notes
Vault Notes are currently a feature available in the Amplenote Unlimited Subscription tier. We appreciate your support building Amplenote into a product that we can build for the rest of our lives! 🙏😊
linkUsing Vault notes
Details about how to create a Vault Note, and how Vault Notes are different than standard notes.
linkWhat is a Vault Note?
A "Vault Note" is a note that gets stored using the Vault Encryption Key, which is never sent to or available to the Amplenote database server.
As described in depth in our technical security documentation, the Vault Encryption Key has the following properties
A random 256-bit Vault Key Salt value is generated and stored in the database encrypted with AES-256-GCM using an encryption key that is not available to the database server and a randomly generated Initialization Vector
The Vault Password entered by the user and the Vault Key Salt are used with PBKDF2-HMAC-SHA256 to produce the 256-bit Vault Key
PBKDF2-HMAC-SHA256 is configured to use 100,000 rounds
A Vault Key Verifier is stored on the server, allowing for a zero-knowledge proof to ensure that the same Vault Password is used for all Vault Notes
linkHow does a Vault Note look/act?
Beyond Amplenote servers never getting the password to decrypt the note's content, there are a few other differences in how Vault Notes are designated and treated in Amplenote.
When you start a new Amplenote session, we do not have access to your Vault Notes. Thus, they will have an icon to indicate they're pending download/indexing in the notes list:
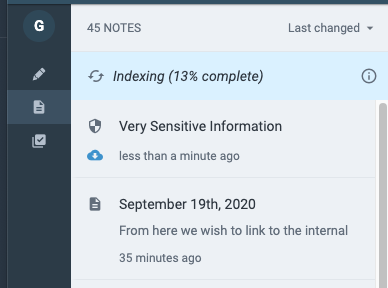
When you open Amplenote in a session where the Vault Note has not yet been provided when opening a note, then all Vault Notes will have the blue icon to indicate they're pending download/indexing
To open the note, click on it and enter your Vault Password in the ensuing popup. Then you can see the note's contents:
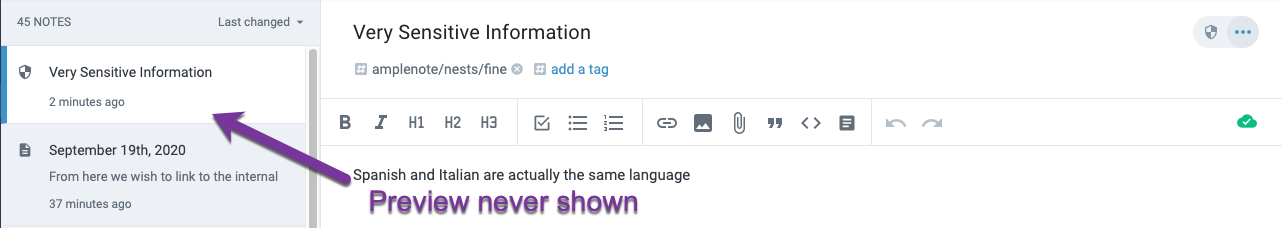
Differences between a Vault Note and standard note: the preview is not shown in Vault Notes, and the Vault Note icon designation once opening the note
Even after decrypting the note, it's contents will never be shown in the note preview. Some other differences between Vault Notes and normal notes:
Cannot be shared with other users
Cannot be made public
Will not display preview content in your notes list
Will not match the content of the note in searches (but will match the title, in Quick Open or search)
Are not included in notebook export (probably destined to change, assuming users vote for it)
If you keep a lot of Vault Notes, your best bet is to tag them and navigate via hierarchy. We're open to updating Vault Notes to be included in search, but for initial implementation we like keeping their obscure.
linkCreating a Vault Note
To make a note into a Vault Note, click the note settings icon on the right-hand side of the note header, then select "Apply Vault encryption" from the menu:
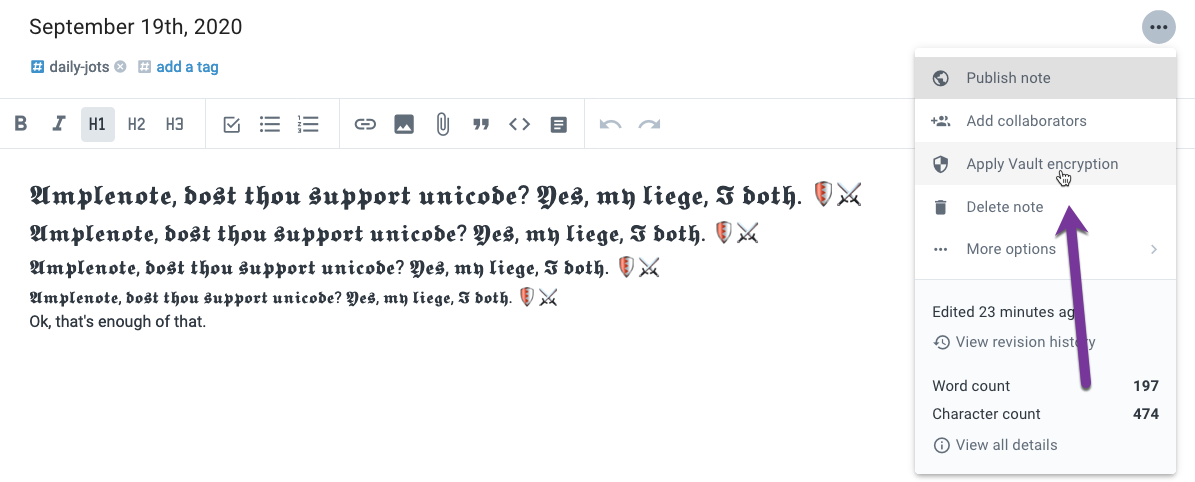
The link to "Apply Vault Encryption"
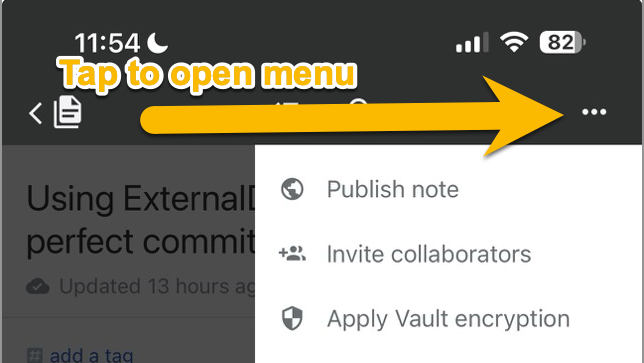
The same option on mobile:
After clicking or tapping to Apply Vault encryption, you will enter your vault password. The content of this note cannot be recovered if you forget your secure password. You must check the box indicating that you understand the note cannot be restored in the event you forget the password, then click the "Secure note" button to secure the note.
We strongly recommend storing your Vault password in a secure note in your password manager of choice (Bitwarden, 1password, Lastpass, etc), so that you will eliminate the possibility of losing it if something hits you hard on the head or whatever.
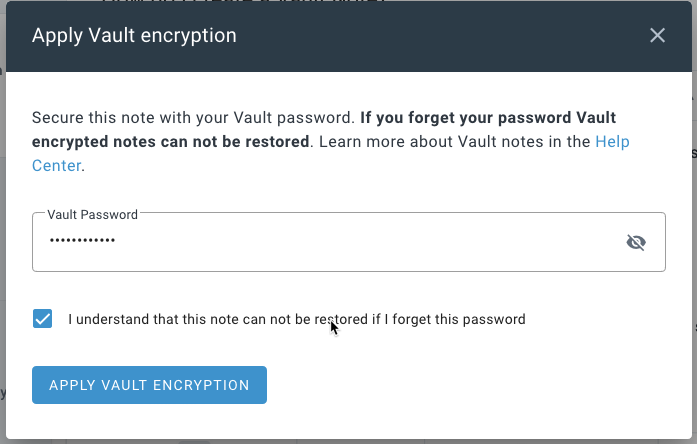
Applying Vault Encryption to a note
Once more: we can not retrieve this password if you lose it. Please store it in your password manager so you can't lose it. If you don't use a password manager, we recommend 1password (very secure) or Bitwarden (good free version).
linkOffline availability
Vault Notes are available offline, so long as you have, at some point, downloaded the note content prior to going offline. It is comparable to standard notes in this regard. Amplenote initially populates the note list with every known note, but the note content gets cached for offline after the initial note content is fetched. Caching Vault Notes to work offline requires providing the Vault Password when prompted.
linkRemoving a Vault Note
To remove a note's designation as a "Vault Note", click "Remove Vault encryption"
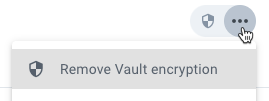
You'll be prompted for your Vault password, after which your note will become a standard note.